Fraud Prevention
Protect yourself from Identity Theft.
Your online security is our
highest priority.
The following information has been provided to help protect you from the many types of financial fraud and identity theft. Select a topic from the tabs to learn how to protect your personal information, how to identify a fraud or scam, and how to report it if you have become a victim of fraud.
Fraud Alerts
Fraudsters are targeting credit union members with fraudulent calls, emails, and texts. BFSFCU will never text, call, or email asking for your personal or account information. Never give out your username, password, or security code.

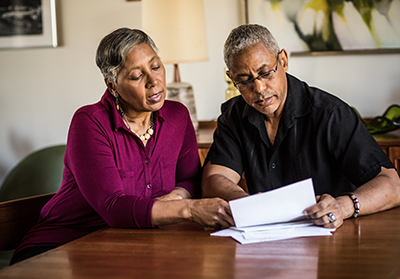
Elder Abuse Awareness
BFSFCU is committed to promoting awareness about the financial exploitation that may occur to the elderly.


Prevent Identity Theft
Learn how to protect yourself from identity theft.

What to do if you're a victim of Identity Theft
Learn how to report a theft of
your identity.

Common Methods used to Steal your Identity
Learn about common ways your personal information can be stolen.

Spoofing BFSFCU Staff
Fraudsters send emails falsely claiming to be from a legitimate company in hopes of luring consumers to a "spoofed" website.

ATM Security
Learn how to protect yourself when using an ATM.

7 Tips for a Safe Trip
How to protect your accounts for a worry-free vacation!

Mail Safety
Learn tips on how to prevent your mail and financial information from being intercepted.

Mortgage Solicitations
BFSFCU will never send mailers requesting members take immediate action regarding their loans.

Protect your Debit and Credit Cards
Learn how to protect yourself from identity theft.

Send Money
Use Zelle® to send money to friends and family, regardless of where they bank.

Fraud Prevention Tips for Students
Keeping your money safe is our top priority, but you play a key role by making sound decisions.
Using Checks Safely
Learn the precautions to take when writing and sending checks.

Website Phishing Scams
Fake webpages are often used to steal and capture personal and financial information from you.

Protect yourself Online
Learn how to reduce the risk that someone will illegally
gain access to your private information or
financial accounts.

Common Methods used to Steal your Identity
Learn about common ways your personal information can be stolen.

Shopping Online Safely
Shopping online can make you an easy target for scammers, consider our tips on how to do so safely!

Gift Card Payment Scams
Gift cards are the most common payment method that scammers seek from their targets, according to the Federal Trade Commission (FTC).

Cryptocurrency Scams
Scammers have turned their attention to cryptocurrencies for one simple reason: payments made in cryptocurrency are difficult to trace.

Amazon Scams
Amazon has been targeted as a favorite to impersonate by fraudsters due to its widespread popularity amongst consumers.

Romance Scams
As more people turn to online dating websites, apps, and social media platforms, scammers have also found these avenues to be lucrative in exploiting individuals.

Job Scams
Job scams can take many forms, but they all prey on the vulnerability of job seekers.

Online Investment Scams
Online investing has become quite common, but if you are
contacted with an investment opportunity that seems too good to be true, it’s likely
a
scam.

Real Estate and Mortgage Wire Scams
One of the latest schemes involves targeting individuals who are in the midst of purchasing a home.

Phone Scams
Phone calls from fraudsters are more than just an annoying nuisance, they are one of the most dangerous type of scams.
IRS and Tax Scams
Have you, or someone you know, received a call from the IRS or the Social Security Administration (SSA) asking for money? Very likely those calls were made by crooks.

Computer Repair and Tech Support Scams
These are most often executed in one of two ways – through unsolicited phone calls or from pop-up warnings on computers.

Charity Scams
By doing your research, you can protect yourself from falling victim to a charity or donation scam and ensure that funds are going to the people that need it.

Advance Fee Scams
Victims are asked to make a small advance or upfront payment for goods, services or financial gain that promises a significant reward that never materializes.
Check Scams
Fake checks are used in many types of scams and the best way to protect yourself is to stay vigilant.

Common Email Scams
Fraudsters send emails pretending to be from legitimate institutions and request sensitive information.

PayPal Scams
Legitimate companies, like PayPal, will never rush or threaten you, or ask for your personal information.

Text Scams
Fraudsters are posing as legitimate entities and sending text messages to obtain your financial information.

How to Help a Victim of a Scam
Learn how to help if you suspect someone you know of being scammed.

What To Do if Scammed
Learn about next steps if you believe you were scammed, gave out personal info or access to devices.